Teams
The Teams feature allows you to group and control user access to associated PagerDuty objects, such as escalation policies, users, schedules, and services. This feature also allows for a customized view in the PagerDuty web app and mobile app that only displays information related to a user’s Team. As an example, security engineers may only want to see users, incidents, schedules and services associated with their Team.
AvailabilityTeams are available on the following pricing plans: Business, Digital Operations (legacy) and Enterprise for Incident Management.
Customers on Professional pricing plans can create up to two Teams.
Please contact our Sales Team if you would like to upgrade to a plan featuring Teams.
Required User Permissions
- Manager, Global Admin or Account Owner base roles can create, edit, and delete Teams.
- Global Admin or Account Owner roles can manage Primary Teams.
- Users with an Account Owner, Global Admin, or Manager base role can set a Team to public or private.
- Users with a Manager Team role can also set the Team’s visibility to public or private.
Create a Team
Product Limits
- You can add up to 100 unique escalation policies per Team.
- There is a limit of 500 users per Team.
- Users can be on multiple Teams, but escalation policies can only be associated with one Team.
- Users can be on up to 400 Teams.
We recommend that you create schedules and escalation policies before creating a Team. When you add an escalation policy to a Team, the escalation policy's users and schedules will be automatically assigned to your Team. Please read Team Association Behavior below for more information.
- In the PagerDuty web app, go to People Teams and click New Team.
- Enter a Name for the Team and optionally add Tags.
- Click Save to continue.
- You will be directed to the Team’s details page. Click Edit Team on the right.
- Search and select the Escalation Policies or Users that you would like to add to this Team.
- Note: When you add an escalation policy to a Team, associated users, schedules and services will be automatically added to the Team, too. You may also optionally add individual users to the Team if they are not on a selected escalation policy.
- Click Save.
Edit a Team
- In the PagerDuty web app, navigate to People Teams.
- To the right of your desired Team, select Edit.
- Make your required edits to the Team's Name, Escalation Policies, Users and/or Tags by searching and selecting them from their fields. To remove escalation policies, users or tags, click to the left of the object.
- Click Save.
Edit Team Roles
Please read Manage Users: Edit Team Roles for more information about editing users' Team roles.
Manage Team Business Service Subscriptions
Please see our section on Subscribe Users and Teams to Business Services for more information about managing Business Service subscriptions.
Delete a Team
- In the PagerDuty web app, navigate to People Teams. and click the to the right of your desired Team.
- To the right of your desired Team, select Delete.
- A dialog will appear that will prompt you to Edit Rulesets, Escalation Policies, Services and Schedules and Reassign Incidents associated with the Team, with the option to reassign incidents to another Team via the dropdown.
- Once you have performed these tasks, click Delete Team.
- Note: This is a non-reversible action and cannot be undone.
Team Association Behavior
Accounts with the Advanced Permissions feature can group PagerDuty objects (e.g., users, schedules, services, and escalation policies) by associating them with a Team. When an escalation policy is added to a Team, the users, schedules and services associated with that escalation policy are also added to the Team. PagerDuty will also determine a user’s access level to Team objects based on their Team role. For example, a user who has a Responder role on a Team will also become a Responder on the Team's associated escalation policies, schedules and services.
In order to maintain consistent access to Team objects, please keep the following in mind:
- If you add a user to an escalation policy or schedule, PagerDuty will automatically add the user to any associated Teams. Note: Users added to a schedule via an override will not inherent the Team's permissions.
- Create a schedule and Update a schedule API:
- Adding users to a schedule via API will add the users to any associated Teams.
- Associating a Team with a schedule via API will add the schedule’s users to the Team.
- Create an escalation policy and Update and escalation policy API: Adding a user to an escalation policy will add the user to any associated Teams. Users may not be removed from the Team if they are still on an escalation policy that is associated with the Team.
Manage Primary Team
TipIn order to set a user’s primary Team, they must already be a member of the Team.
Some organizations may want users to have primary teams for billing purposes. To designate a user's primary team:
- In the PagerDuty web app, navigate to People Users and click the desired user's name.
- Select the tab Permissions & Teams and click Edit in the section Teams and Team Roles.
- On the modal that appears, search and select a primary team for the user. You may also remove the primary Team by clicking .
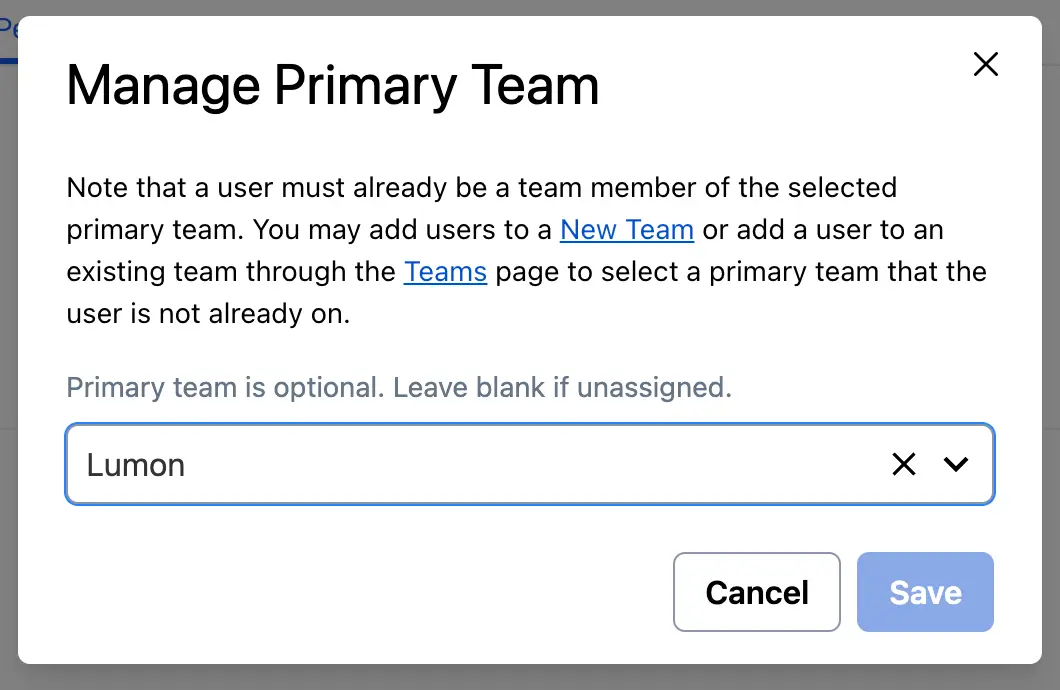
Manage primary team
- Click Save.
You will now be able to see the user's primary team in the Teams & Team Roles section.
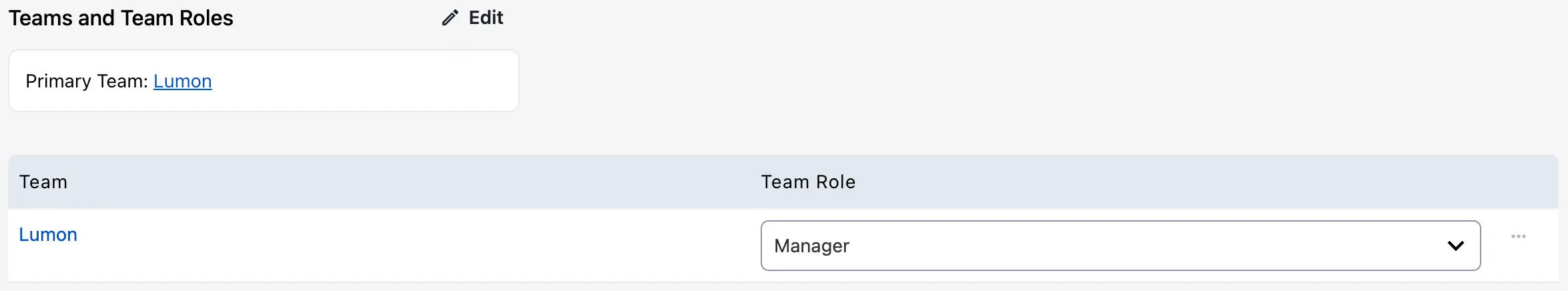
Primary team on the user profile
Filter by Team
The Team filter dropdown is available on most PagerDuty objects in the web app, such as the Incidents page, Service Directory, Users, Escalation Policies, Insights, etc.
To filter the UI by Team, in PagerDuty web app click the Team dropdown. You can choose to view All Teams, My Teams, or select specific Team(s).
When you select a Team filter on one page, the filter will stay in effect as you navigate to other pages. For example, to quickly see all users in a Team, go to the Team dropdown menu and select your preferred Team, and then go to People Users. You will only see users associated with the selected Team.
Your filter selection will not impact the view that other users see in their accounts.
Team Filtering BehaviorTeam filter results may vary between the Incidents list and Insights reports because each view evaluates Team associations differently. The Incidents list tracks every Team an incident has been associated with throughout its entire lifecycle, whereas Insights and Analytics filter strictly by the Team currently associated with the incident's service at the time the report is generated.
Consequently, if a service has been reassigned to a different Team after an incident has been triggered, that incident may appear under its original Team in the Incidents list but under the new Team in Insights. This is expected behavior and typically occurs following service reassignments or changes to an escalation policy’s Team association.
Team Privacy
With Advanced Permissions, Teams have the option to be set to Private or Public. By default, all Teams are public.
- Public: Teams can be viewed and accessed by users outside of those Teams.
- Private: Teams cannot be viewed and accessed by users outside of those Teams, except for users with Global Admin or Account Owner base roles. Global Admins and the Account Owner have access to all private Teams.
When a Team is set to private, users who are not part of that Team:
| Will not Be Able To | Will Be Able To |
|---|---|
| - View the Team’s schedules, escalation policies, services, and incidents - View Event Orchestrations associated with the Team - Find the Team’s service or escalation policy when creating a new incident - Find the Team’s escalation policy when reassigning or adding responders to an incident - Find the Team when adding subscribers to an incident - Find the Team on the Team lens dropdown, on the People Teams page, or on the profile page of a user associated with the Team | - Find users associated with the private Team on the People Users page - Find users on the private Team when creating, reassigning, adding responders, or adding subscribers to an incident - Find users on the private Team when creating a schedule override |
Note: Team privacy does not currently apply to the following pages or configuration objects:
- Incident Workflows
- Postmortems
- Analytics
Known IssuesDepending on the method used, there are some known inconsistencies related to incidents' visibility when a service is added to a private Team.
Method 1 (Recommended): If an admin changes a service's existing Team's visibility from public to private, incidents associated with the private Team's service and escalation policy will only be available to members of the private Team, Global Admin users, and the Account Owner (i.e., privileged users). This is the expected behavior.
Method 2: If an admin changes a service's existing, public Team to a different, private Team, the old Team's incident permissions will govern the visibility of historical incidents. This has the effect that already existing incidents will remain visible to non-privileged users on the Incidents overview page, as well as on incidents' detail pages.
Method 3: If an admin associates a service, which currently does not have a Team, with a private Team, historical incidents will be visible to non-privileged users on the Incidents overview page, however they will not be able to view incident details.
Edit Team Privacy
- To edit a Team’s privacy, navigate to People Teams and select your desired Team.
- Navigate to the Users tab on the Team’s page and set External Visibility to either Public or Private.
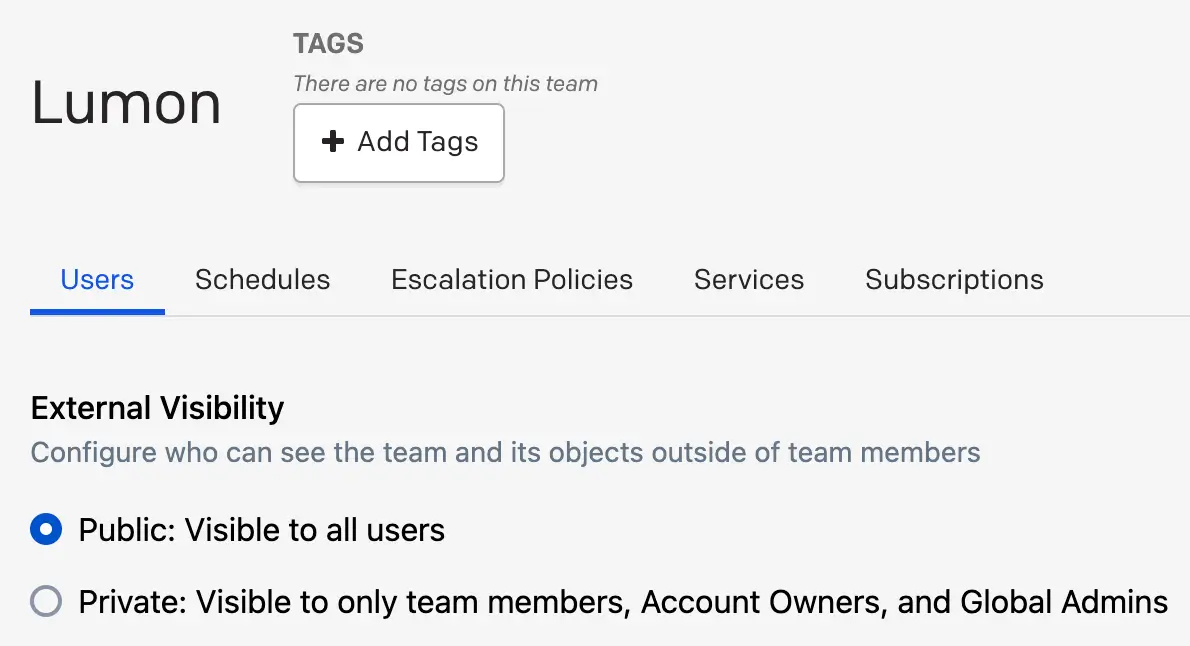
Team visibility
Respond to Incidents From Other Teams
The Team that an incident is associated with is based on the service where the incident was triggered. For example, if an incident is triggered on a service associated with the Network Operations Team, then the incident will be associated with the Network Operations Team. If the incident is reassigned to an escalation policy or user that belongs to a different Team, then the incident will still be associated with the Network Operations Team.
Any users who are assigned to the incident will be able to respond to it, even if they are not associated with the Network Operations Team. These users must be directly assigned to the incident to take action on it. They will show up under Assigned to when viewing the incident in the web app, or Assignees in the REST API. However, they won’t see the incident on their Incidents dashboard if filtering by My Teams.
Any users who are not assigned to the incident AND who don’t have access to respond to incidents associated with the Network Operations Team (e.g., a user with an Observer or Restricted Access base role and no Team role or object role on the Network Operations Team or its associated objects) will not be able to respond to the incident.
With that in mind, if there is a user who needs to be able to respond to incidents for all or multiple Teams, make sure that the user has any of the following role configurations:
- A Responder base role. This will allow them to respond to incidents associated with any Team.
- A Responder or Manager role on any Team for which they need to respond to incidents.
- A Responder or Manager object role on any service for which they need to respond to incidents.
Rest API Access
All users can create personal REST API keys that match their user permissions. For example, a user with a Manager base role can create a personal API key that will allow them to edit a schedule. However, they will not be able to add new users to the account because a Manager base role does not allow this.
Global Admins and the Account Owner can create and manage global API access keys, which typically offer more API access than user-specific API keys.
Updated 27 days ago
