Email Integration Guide | PagerDuty
This guide describes how to integrate PagerDuty with any service capable of sending an email. Please note that we offer integration guides and plugins for many popular monitoring services. Furthermore, tools that don’t yet have dedicated guides can often be integrated with PagerDuty using our Events API.
How it Works
Events and alerts from monitoring tools will be sent as emails to your desired PagerDuty integration email address. PagerDuty will open and trigger an incident when it receives an email to this integration address.
Requirements
- You must have a User, Admin, Manager, Global Admin or Account Owner role to configure the integration.
- Your monitoring tool must be able to send emails.
- One of the following integration types in PagerDuty:
- Event Orchestration: Integrating with Event Orchestrations may be beneficial if you want to build nested rules based on the events coming from the integrated tool.
- PagerDuty Service: Integrating with a PagerDuty service directly can be beneficial if you don’t need to route alerts from the integrated tool to different responders based on the event payload. Note: Email integrations at the service-level are not evaluated by Service Orchestrations. Instead, you can configure rules and filters to manage these events.
Integration Walkthrough
You can use the following methods to integrate with PagerDuty via email:
Integrate with Event Orchestration
- In the PagerDuty web app, navigate to AIOps Event Orchestration.
- Select your desired Global Orchestration and then click Integrations.
- To the right of the field Email Address, click Copy to Clipboard and refer to your monitoring tool’s documentation on connecting with an email address in order to complete the integration. PagerDuty will open and trigger an incident when it receives an email to this integration address. The Email Incident Example section displays a screenshot of what a test incident will look like.
Integrate with a PagerDuty Service
Event OrchestrationService Orchestration rules are not applied to service-level email integration events. If you would like to utilize Orchestration rules with email events, please integrate directly with an Event Orchestration.
- In the PagerDuty web app, navigate to Services Service Directory.
- Click the name of the service you want to add the integration to. Then select the Integrations tab and click Add an integration.
- Search and select Email from the dropdown Select the integration(s) you use to send alerts to this service.
- Click Add to save your new integration. You will be redirected to the Integrations tab for your service.
- Find your integration in the list and click to the right. Copy the Integration Email address and refer to your monitoring tool’s documentation on connecting with an email address in order to complete the integration. PagerDuty will open and trigger an incident when it receives an email to this integration address.
Edit an Email Integration Address
You can customize an email integration's username in the PagerDuty web app:
- Navigate to Services Service Directory and select your desired service from the list.
- Select the Integrations tab and click to the right of the email integration.
- In the Integration Email section, click and enter a new value.
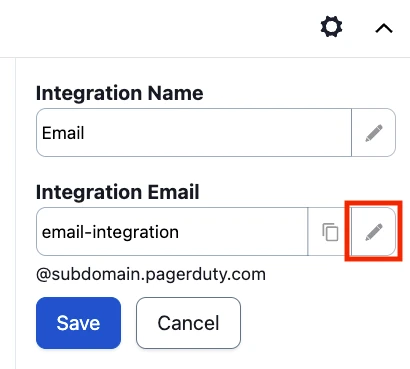
Edit email integration address
- Click Save.
Email Incident Example
Below is a test incident triggered via email:
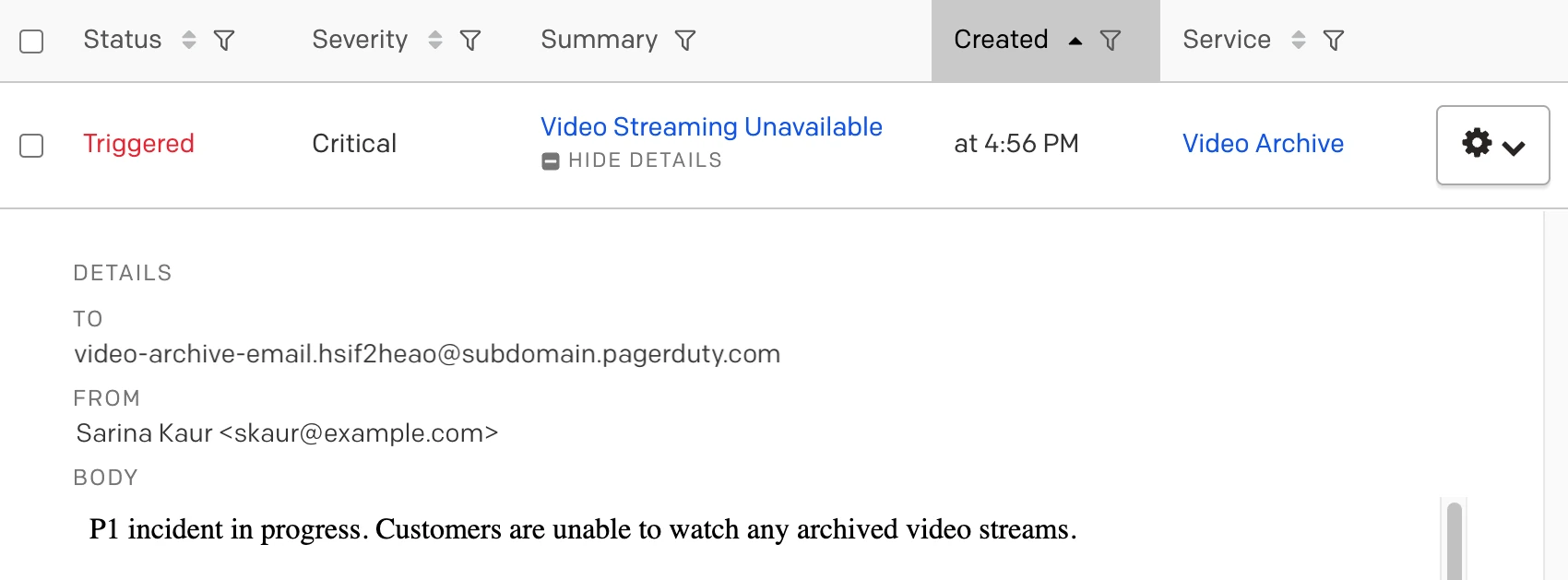
Email incident
Email Management
RequirementThe following instructions are for service-level email integrations. If you are integrating with an Event Orchestration, please refer to our Event Orchestration article for guidance on managing email events.
By default, PagerDuty opens a new incident every time an email is received at the integration address. You can change this behavior by changing the Email Management setting for your service. See Email Management: Filters and Rules for more information.
Email Filters
Filters allow you to disregard certain messages arriving at the integration email address. Each email’s subject, body, and from address can be checked against either a safelist or blocklist regular expression filter. Messages that don’t pass the filter will be silently discarded. This feature is handy if you have a monitoring tool that sends out emails that you don’t want to trigger incidents in PagerDuty. See Email Filters for more information.
TLS Encrypted Emails
PagerDuty email servers are configured to accept TLS-protected SMTP sessions when your outbound mail servers are configured to use TLS opportunistically. When the message is encrypted, the last hop listed in the receive headers will mention a TLS-enabled connection.
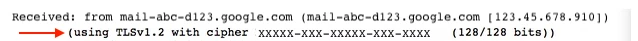
TLS encrypted email
Email Requirements and Behavior
Email Encoding
Emails sent to an email integration endpoint must be sent in UTF-8.
Email Attachments
If your email (including headers, attachments, etc.) is under 96 KB, the message can pass through without truncation. However, PagerDuty will strip all attachments from emails and truncate messages if the email is over 96 KB. In those cases, the following can happen:
- Any parts of the email body where the Content-Type does not match the following regular expression will be discarded:
/(text\/(plain|html)|multipart\/)/
This means PDF files and similar attachments will be stripped. - Text parts (i.e., Content-Type of
text/plainortext/html) will be truncated to 32 KB. - If the resulting total email size including headers, attachments, etc. still exceeds 2 MB then PagerDuty will reject the message.
You can tell if a message has been truncated or had attachments removed by checking for the headers X-PagerDuty-Truncated-Part or X-PagerDuty-Removed-Attachments when viewing the raw message. You can view the raw message on the incident's detail page by clicking View Message on an incident log entry, then View Raw Message.

Truncated email
See Email Notifications for more details on email content and behavior.
Email Size Limits
If an email is over 10 MB (including headers and attachments), our server will reject it. This rejection happens prior to any processing or truncation. The email server which sent the message will receive an error notification indicating that the "Message size exceeds fixed limit".
If an email is still over 2MB after truncation and being stripped of headers and attachments, it will be silently dropped and your server will not receive a notification.
Incident Key Truncation
If the incident key of the email that triggered an incident is more than 255 characters, it will be truncated to 255 characters.
Truncation of Incident Details in Email Notifications
When you receive a PagerDuty email notification, the Details section of each incident will be truncated to 500 characters. You can access the complete email body in the PagerDuty web app via the incident logs and details, or via the PagerDuty Mobile App.
Email Event Ingestion Limit
Email events have an ingestion rate limit of 60 events/min, per key. If you require a higher limit, please contact your account team or consider using the Events API, which supports higher rate limits and can be increased even further for PagerDuty AIOps customers.
Updated 2 months ago
